Professor
ProfessorLogicMonitor Portal Security
These articles:
- https://techcrunch.com/2023/08/31/logicmonitor-customers-hit-by-hackers-because-of-default-passwords/?guccounter=1
- https://www.bleepingcomputer.com/news/security/logicmonitor-customers-hacked-in-reported-ransomware-attacks/
...indicate that some LogicMonitor accounts may have had weak default passwords applied and become compromised.
Until we have an official word from LogicMonitor, may I suggest that all LogicMonitor administrators:
- Delete or suspend any users that should not be in your system
- Ensure that no “out of the box” accounts are Active (including the lmsupport account)
- You should set this account to “Suspended” until we have word that this account is not affected
- Note that unless this account is Active, LogicMonitor Support cannot access your portal
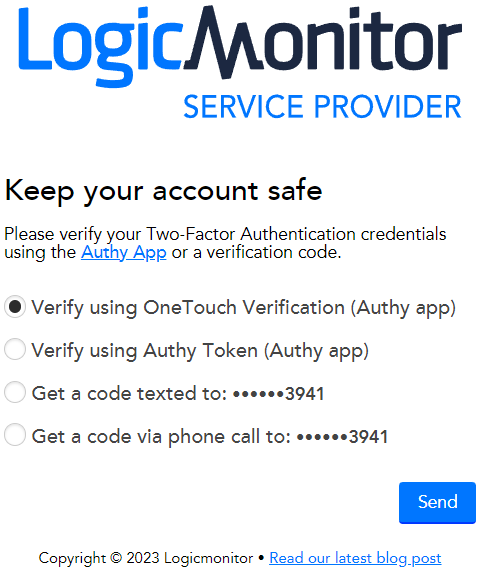
- Enable 2FA for ALL users
- I mean, you did that already, right? RIGHT?
- IMPORTANT: You need to do this for administrator users, even if you have SSO
- Ensure that any user that has not logged in recently (say for 60 days) is either deleted or set to Suspended
- IMPORTANT: Revoke administrator/manager rights from anyone that does not absolutely need them
- The recommendation is 2 users per LogicMonitor portal
- If you don’t recognise a user, seriously consider setting it to Suspended
- Be cautious of System Integration accounts - you may disrupt these if you are not careful
- If a system has access, ensure that this via an API user, not an Access Token on a named person.
I will update this post with other suggestions as they are made.
We can confirm that LogicMonitor is currently investigating a security incident that affected a small number of customers, and we are taking all necessary and recommended steps to mitigate any impact. All known affected customers have already been notified, and we are working with these customers to take preventative measures. We recommend all customers take the time to secure their accounts with the already available feature sets available in customer portals, such as mandating 2FA. Here is the Two-Factor Authentication Setup Guide.
If you aren’t familiar with the configuration of these settings, we will be happy to connect you to support for further assistance